|
Let see the catalog of software app downloads! Our catalogue has a lot of software, free programs, demonstration, and demo versions PC solutions to settle in different classes. The Softempire catalog is certainly free of charge to test. Move for awesome program systems and spend sparingly your time! Browse the free of charge download exclusive program catalogue: system programs and applications, file security programs, backups, and many varied attractive applications. Have a look on the great software utilities plenty on Softempire.com: there millions of amazing and good programs waiting for you.
Computer software utility free download catalog! Pick an app!
System software for development, direction, and support of your computer best patterns.
Hard drive utility tools for laptop health and PC wealth.
Utility software for Mac reviews champions! Get the maximum from your Mac with SoftEmpire!
|
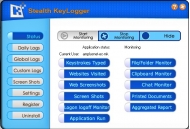
Stealth KeyLogger
|
|
Download
|
Buy now!
|
View screenshots
|
Vendor Price: $ 39.95
License: Shareware
File Size: 3.49 Mb
Version: 5.0
Release Date:
5 Dec 2008
OS: WinNT 4.x, Windows2000, WinXP, Windows2003, Windows Vista Starter, Windows Vista Home Basic, Windows Vista Home Premium, Windows Vista Business, Windows Vista Enterprise, Windows Vista Ultimate
System Requirements:
Win2000/XP/2003
Company: Amplusnet
|
|
Stealth KeyLogger is an invisible, easy to use surveillance application, designed to monitor and record all activities on a computer.
Perfectly suited for both office and home use Stealth KeyLogger offers detailed information on who uses your computer, their e-mails and chat conversations, the visited web sites, programs run as well as actual screenshots of their activity, websites visited and keystrokes history.You can schedule the exact period when you want that Stealth KeyLogger to monitor or, you can choose to exclude users from monitoring, and to specify when should the application record an user as being IDLE. On the other side there are new functionalities improved from the previous ones for a better surveillance in a better stealthy way.
This keylogger keeps up with the technology progress, so that the version of Internet Browsers and Instant Messaging applications does not influence the results of the application.
Reports are organized chronologically, always providing information on user, application and content (keystrokes, websites etc) and presented in a easy to read web format. For security reasons, reports may be printed or sent to a specified e-mail address. The improved email reporting gives you the liberty to choose which type of report you want to be send on e-mail, making the surveillance easier. You can also sent logs via Ftp, or save them to LAN. Stealth Keylogger can delete the old logs if the size specified is exceded.
Stealth KeyLogger has a hotkey and password activation protection and runs in stealth mode being undetectable in Task Manager (applications and processes). To save disk space, the program can clear logs periodically or after sending them to you.
|
More to download:
ZOC
This terminal emulator gets you connected via telnet, SSH/SSH2, modem and ISDN. It is well known for it's outstanding user interface. High configurability powerful scripting and a wealth of features make ZOC a great tool to access Unix shells.
LastBit Yahoo Messenger Password Recovery
Password recovery tool for Yahoo Messenger. Yahoo Messenger Password cracks stored login information for the current computer user. No professional knowledge or experience is required.
USB Safeguard
USB Safeguard is a portable software that allows you to protect your private files with a password on your removable drive using the secure AES 256 bits key. Supports USB flash drive, HDD hard drive, SSD, memory card and others.
|
|
|
Windows Backup |
Looking for backup software? Try Handy Backup - automatic data backup to DVD, CD, FTP, network, or Online. Client-server enterprise backup software.
|
|
Top Downloads |
Freeware program to rename files & folders & Multimedia files wi
Hotspot Shield secures your Internet connection from hackers
Protect your computer from viruses and malicious programs.
|
|

