| Editor's choice |
Enstella Best EDB to PST Tool
Enstella EDB to PST Tool-best EDB File Recovery program to recover EDB to PST
AEVITA Save Flash
AEVITA Save Flash lets you easily save flash movies right from Internet Explorer
Incredimail to EML Converter
Incredimail to EML Converter to convert Incredimail to EML Files
Telekomat .NET
Revolution for Bandwidth Monitors. Monitor and optimize your network connection.
ABS Mailbox Monitor
Monitors email boxes and sends a text message to your cell phone to alert you...
WinMHT
Save collections of complete Web pages to a single Web archive. Browse offline..
How to Split .PST
How to Split .PST files? Get the solution with SysTools Split PST Software
|
|
Free software tool downloads from the most popular in download webs sites! Browse the called for software applications classes, learn the most recent updates of the notable programmes, and try directly! Do not toss away a luck to get the best software: utilise SoftEmpire website to obtain software applications for free of charge. Meet the catalog of freeware and software app demo versions. Search among operating system utilities programs, setup managers, firewalls, and all other kinds of software apps for your computer or mobile stuff!
Listing of internet server software. Any king of server software with free download from vendors. FTP/ SFTP/ TFTP servers, mail servers, firewalls for any kind of servers and other server software. Part of listed software is free of charge. Best free server software in our list!
|
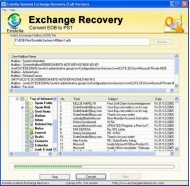
Perfect EDB Recovery
|
|
Download
|
Buy now!
|
View screenshots
|
Vendor Price: $ 299
License: Shareware
File Size: 1.28 Mb
Version: 2.0
Release Date:
18 Jan 2011
OS: Win2000, Win7 x32, Win98, WinServer, WinVista, WinXP
System Requirements:
Pentium II 400 MHz, 64 MB RAM, 10 MB
Company: Perfect EDB Recovery
|
|
If you lost your vital Exchange data due to logical or physical corruption in you MS Exchange server and you need to safely get back your Exchange Database then instantly download Enstella Perfect EDB Recovery program which definitely gives you positive results by recovering your entire EDB mailboxes form corrupt exchange database in just few moment. Fast scanning processes of EDB to PST tool easily recognize corrupted or damaged EDB files and then successfully restore Exchange Mailbox to PST.
The best EDB to PST converter tool is specially design to handle any kind of Exchange server corruption such as-
*Virus Attack
*Software Failure
*Hardware Failure
*Jet engine error
*Header corruptions
*File Size error etc
In these kinds of situations Enstella Perfect EDB recovery tool safely and securely recover Exchange Priv1.EDB files or Pub 1.EDB file of different MS Exchange server -5.0, 5.5, 2000, 2003 and 2007. Export EDB to PST easily migrate exchange mailboxes into PST with EDB mailbox items such as- contacts, journals, notes, task, appointments etc.
Most appropriate features of Enstella Perfect EDB recovery software-
*Instantly recover EDB file and convert EDB file to PST file.
*EDB to PST tool easily repair corrupt exchange database and exchange mailbox to PST
* recover EDB mailbox to PST with their items- contacts, journals, notes, tasks, deleted items from deleted folders etc.
*Safely extract Exchange Database form MS Exchange server-5.0/ 5.5/ 2000/ 2003/ 2007.
*Provided full and demo version of software.
*Simple and easy to understand its working operations
Install free demo/trial version of Perfect EDB to PST software for instant recovery, it will show you whole EDB mailbox items list and if you are eligible to view recover EDB files then install full version software and convert EDB files to PST file.
|
More to download:
Transfer Lotus Notes Contacts
Now you can easily transfer Lotus Notes contacts with highly advanced Lotus Notes contacts to Gmail software. Software converts all Lotus Notes contacts saved in names.nsf file to CSV file and easily import CSV files in Google Apps.
Exchange Export EDB to PST
Exchange Export EDB to PST tool to recover Exchange EDB to PST and export Exchange mailbox to PST. Best Exchange EDB to PST exporter for converting Exchange EDB to PST and exporting EDB to PST speedily. Most safe as Exchange EDB export PST software.
Great EDB to PST
Convenient EDB to PST Recovery utility instantly recover EDB fie to outlook PST file with existing emails Meta data like-cc/bcc/subject/date and time etc in proficient manner and easily restore them into outlook file.
|
|
|
Windows Backup |
Looking for backup software? Try Handy Backup - automatic data backup to DVD, CD, FTP, network, or Online. Client-server enterprise backup software.
|
|
Top Downloads |
Schedule, resume and accelerate downloads by up to 5 times with this accelerator
FrostWire - Download MP3s, Videos & Movies for FREE
Log into web sites with a single click. Fill web form details automatically.
|
|

